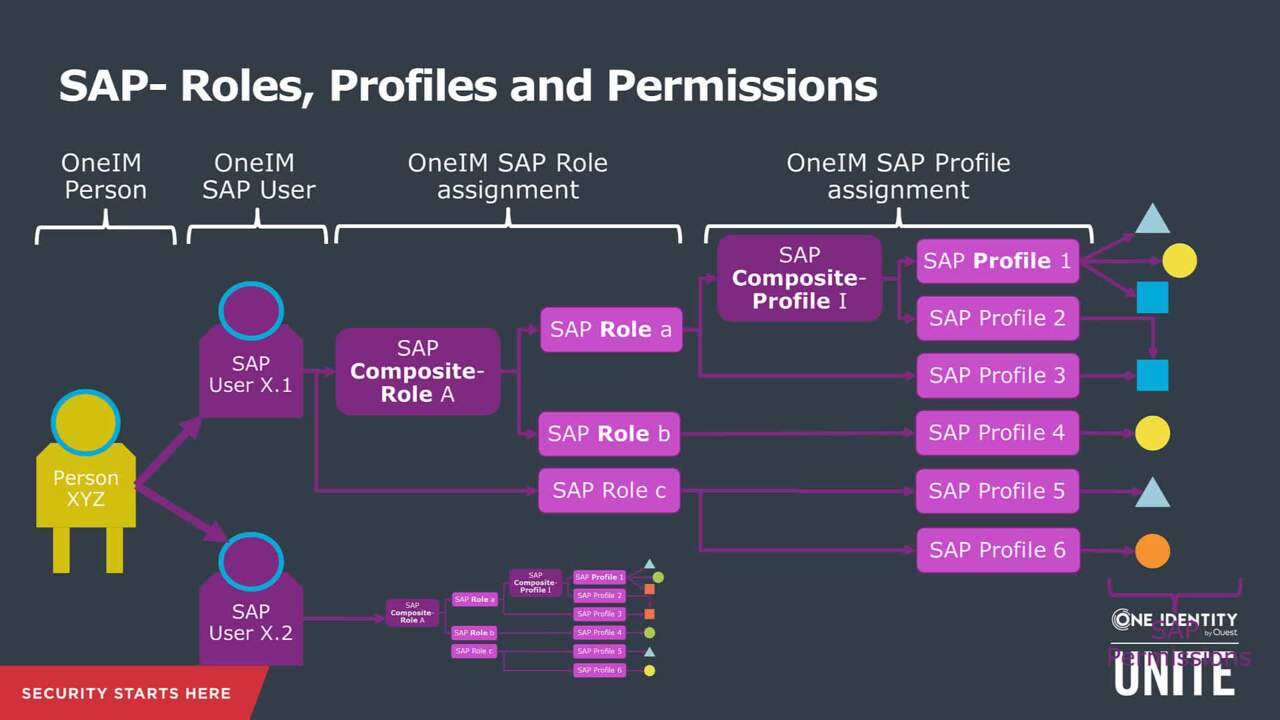
Identity Management and SAP Users, Roles and Transactions - Part1 - IBM Security Identity and Access

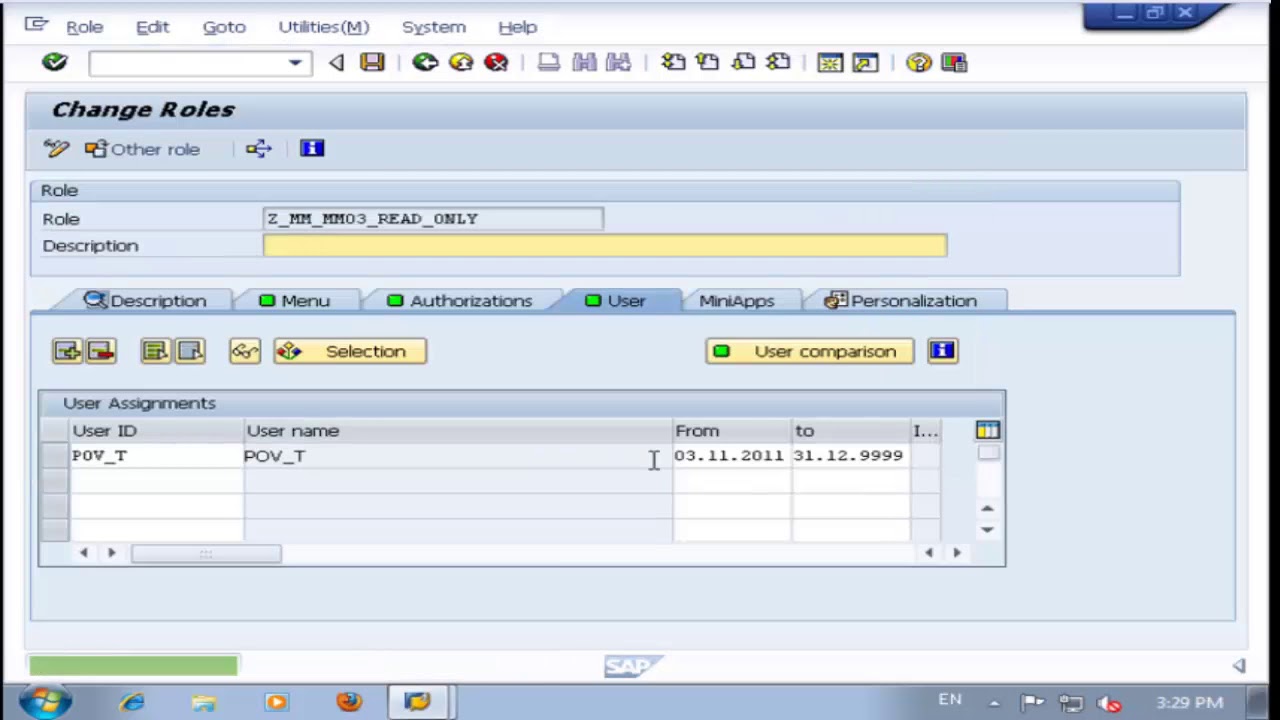
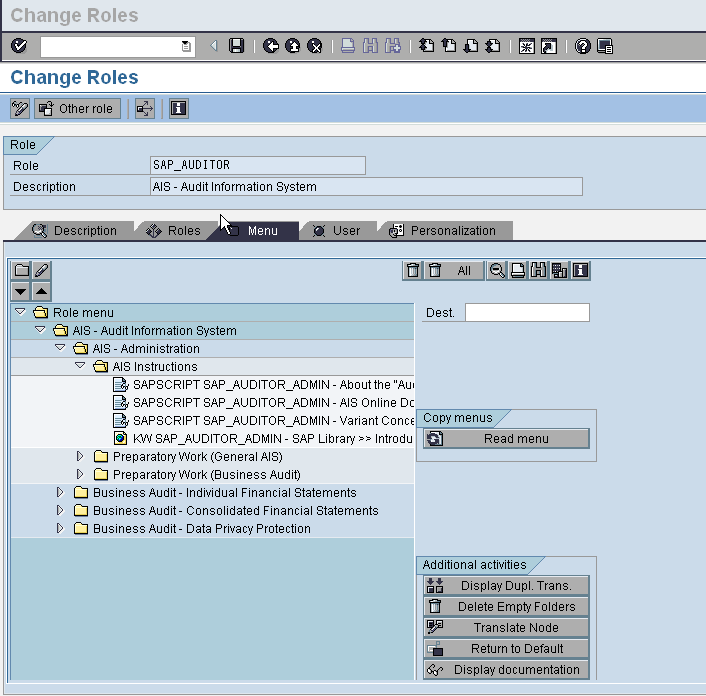
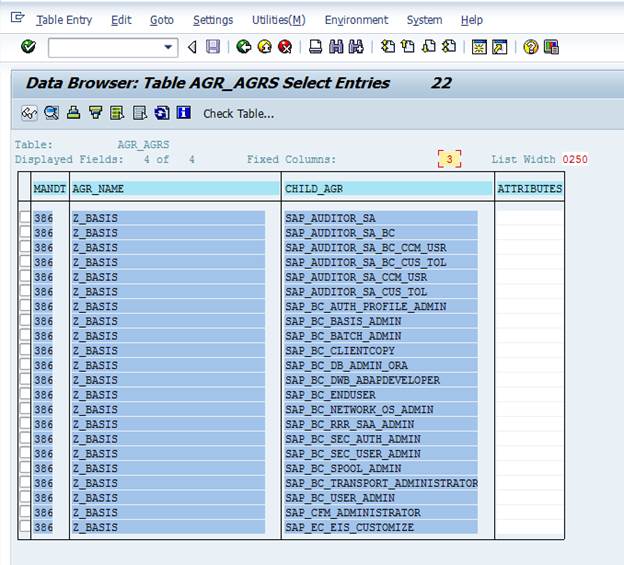
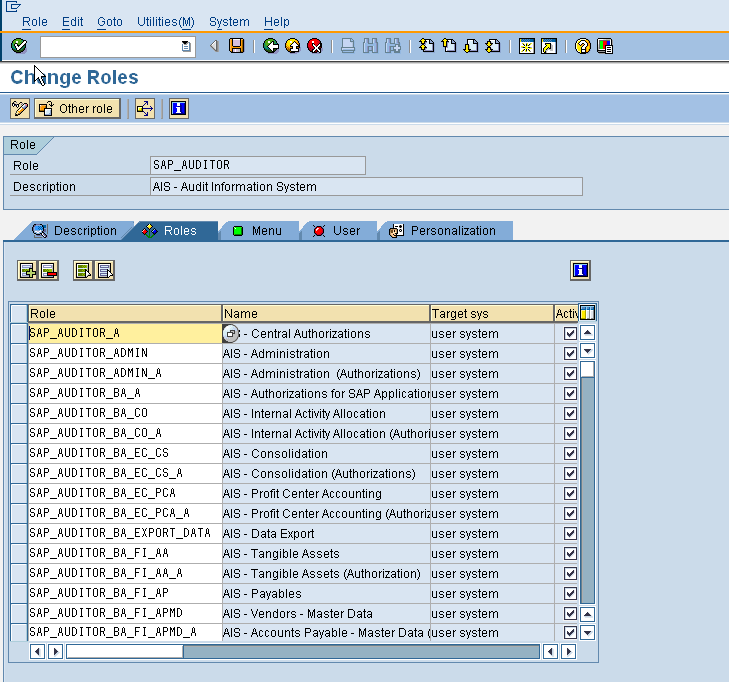
SAP Basis For Beginner: How to search for composite role by using single role that attached to it and vice versa

Identity Management and SAP Users, Roles and Transactions - Part1 - IBM Security Identity and Access